Join us in the Black Hills InfoSec Discord server here: [ Ссылка ] to keep the security conversation going!
🏫 Learn Introduction to Python with Joff Thyer from Antisyphon
[ Ссылка ]
00:00 - FEATURE PRESENTATION: Part 1
00:28 - About Joff
01:44 - Scenario
03:46 - What is shellcode
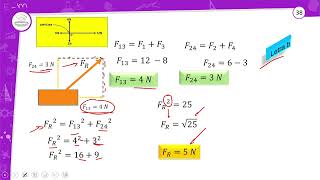
05:44 - Python3 – ctypes module
06:59 - Python3 – ctypes windll object
08:37 - Windows Architecture
10:50 - Passing Arguments to WinAPI Functions
12:11 - Some types from ctypes module
12:39 - Specifying Required Argument Types
14:08 - WinAPI data types and constants
15:06 - the ctypes module also has wintypes
15:51 - Example function prototype
17:54 - Shellcode Execution using Windows API
20:05 - The Myriad of Ways you get BUSTED
23:23 - Machine Architecture Matters
Description: Imagine you are pen testing a company and gain access to a Windows application server. You discover the server has application allow listing deployed, and strong EDR/XDR defensive solutions. To your excitement, you find there is a Python interpreter installed. It would be really great if you could use that Python interpreter to execute your favorite C2 framework shellcode and use all of your normal hacking toolsets to continue your work. With a little bit of coding work, you can! In this Black Hills Information Security (BHIS) webcast, you will learn exactly how to achieve your goal of shellcode execution with Python.
Tiny repo with demo code:
[ Ссылка ]
Slides
[ Ссылка ]
Part 2
[ Ссылка ]
Part 3
[ Ссылка ]
Black Hills Infosec Socials
Twitter: [ Ссылка ]
Mastodon: [ Ссылка ]
LinkedIn: [ Ссылка ]
Discord: [ Ссылка ]
Black Hills Infosec Shirts & Hoodies
[ Ссылка ]
Black Hills Infosec Services
Active SOC: [ Ссылка ]
Penetration Testing: [ Ссылка ]
Incident Response: [ Ссылка ]
Backdoors & Breaches - Incident Response Card Game
Backdoors & Breaches: [ Ссылка ]
Play B&B Online: [ Ссылка ]
Antisyphon Training
Pay What You Can: [ Ссылка ]
Live Training: [ Ссылка ]
On Demand Training: [ Ссылка ]
Educational Infosec Content
Black Hills Infosec Blogs: [ Ссылка ]
Wild West Hackin' Fest YouTube: [ Ссылка ]
Active Countermeasures YouTube: [ Ссылка ]
Antisyphon Training YouTube: [ Ссылка ]
Join us at the annual information security conference in Deadwood, SD (in-person and virtually) — Wild West Hackin' Fest: [ Ссылка ]
#redteaming #cybersecurity #python #redteam
Part 1: Shellcode Execution with Python | Joff Thyer
Теги
Black Hills Information SecurityBHISJohn StrandInformation SecurityInfosecRed TeamPenetration TestingPentestingPentesterHackerHackingHackersEthical HackingBlue TeamCybersecurityDigital ForeniscsDFIRIncident ResponseIncident HandlingWindows LoggingSysmonATT&CKKill ChainsBSidesSecurity WeeklyWild West Hackin FestWWHFHoneybadgerADHDCyber DeceptionActive DefenseActive CountermeasuresDocker








![Гипертоническая болезнь - Причины развития - Часть 2 [S06E05]](https://s2.save4k.ru/pic/TZhTRRkwKcE/mqdefault.jpg)