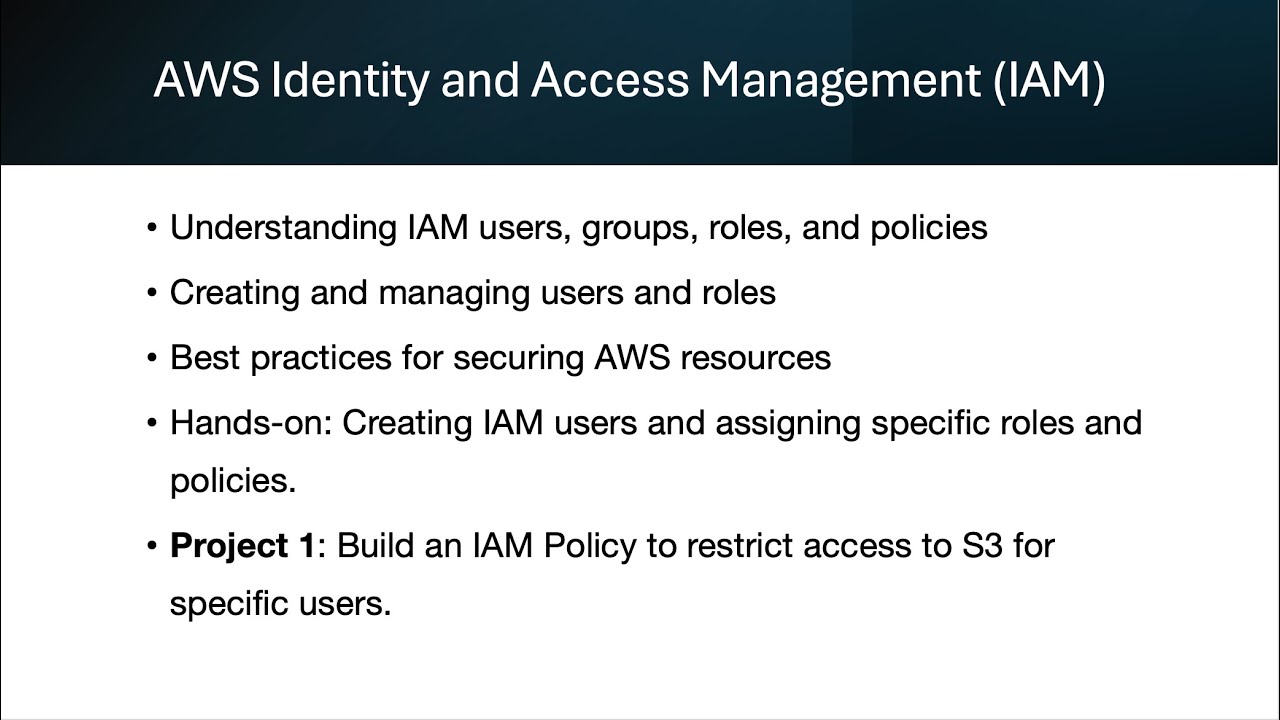
AWS Identity and Access Management (IAM) allows you to manage access and permissions for AWS resources securely. By using IAM, you can control which users or services have access to AWS resources and specify what actions they can perform. The main concepts of IAM include users, groups, roles, and policies. IAM users are individual entities that can have access credentials to interact with AWS resources. Groups, on the other hand, are collections of users that inherit permissions applied to the group, simplifying management. IAM roles are special entities that enable AWS services to assume permissions without needing long-term credentials. Policies, which are written in JSON, define what actions are allowed or denied for users, groups, or roles.
Creating and managing IAM users and roles is straightforward. You can create users with either programmatic access (for APIs and CLI) or console access, and assign them permissions by adding them to groups or attaching policies directly. When it comes to IAM roles, you can create a role, assign policies, and then attach it to an AWS service like EC2 or Lambda, allowing the service to interact with other AWS resources such as S3.
IAM security best practices include enabling Multi-Factor Authentication (MFA) for privileged users, following the principle of least privilege, and avoiding the use of the root account for daily operations. Rotating credentials regularly and using IAM roles for applications instead of embedding access keys is highly recommended. Additionally, using AWS CloudTrail for auditing all IAM activities helps track and log suspicious behavior.
Hands-on exercises, such as creating users and assigning roles, help to deepen the understanding of IAM. By assigning specific policies and testing access to AWS resources, users can ensure their IAM configurations are secure and functioning as expected.