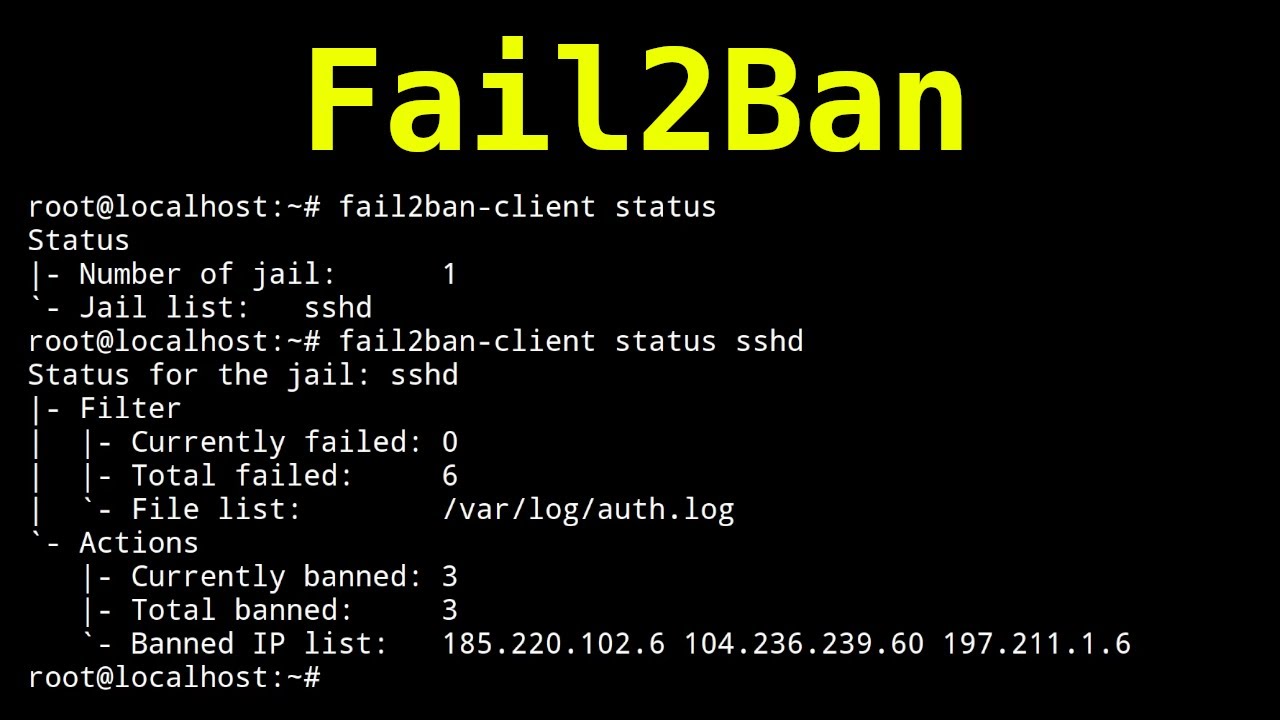
Hey guys! in this video I will be showing you how to setup SSH brute-force protection with Fail2Ban on Linux. Fail2ban scans log files (e.g. /var/log/apache/error_log) and bans IPs that show the malicious signs -- too many password failures, seeking for exploits, etc. Generally, Fail2Ban is then used to update firewall rules to reject the IP addresses for a specified amount of time, although any arbitrary other action (e.g. sending an email) could also be configured
This video is sponsored by Linode, use the link below to get 20$ in free credits.
[ Ссылка ]
Promo code: HACKERSPLOIT20
◼️Get Our Courses:
Python For Ethical Hacking: [ Ссылка ]
Ethical Hacking Bootcamp: [ Ссылка ]
◼️Our Platforms:
Blog: [ Ссылка ]
HackerSploit Forum: [ Ссылка ]
HackerSploit Cybersecurity Services: [ Ссылка ]
HackerSploit Academy: [ Ссылка ]
HackerSploit Discord: [ Ссылка ]
HackerSploit Podcast: [ Ссылка ]
iTunes: [ Ссылка ]
◼️Support us by using the following links:
Patreon: [ Ссылка ]
I hope you enjoy/enjoyed the video.
If you have any questions or suggestions feel free to post them in the comments section or on my social networks.
Social Networks - Connect With Us!
-------------------------------
Facebook: [ Ссылка ]
Twitter: [ Ссылка ]
Instagram: [ Ссылка ]
Patreon: [ Ссылка ]
--------------------------------
Thanks for watching!
Благодаря за гледането
Kiitos katsomisesta
Danke fürs Zuschauen!
感谢您观看
Merci d'avoir regardé
دیکھنے کے لیے شکریہ
देखने के लिए धन्यवाद
Grazie per la visione
Gracias por ver
شكرا للمشاهدة
#Linux#Hacking